SSO Setup
Last updated: May 5, 2026
Configure Single Sign-On (SSO) and Just-In-Time (JIT) user provisioning for your organization.
Overview
Supported Identity Providers include:
Google Workspace
Okta
Microsoft Entra ID (Azure AD)
OneLogin
Any SAML 2.0-compliant Identity Provider
Prerequisites
Before setting up SSO, ensure you have:
Admin access to your Iris organization settings
Admin access to your Identity Provider
Your Identity Provider's SAML metadata URL or XML
Your organization's email domain (e.g., acmecorp.com)
Setting Up SSO
Go to Settings > Security
Click the "+ Setup SAML SSO" button to begin. Iris will provide you with three values to enter into your Identity Provider:
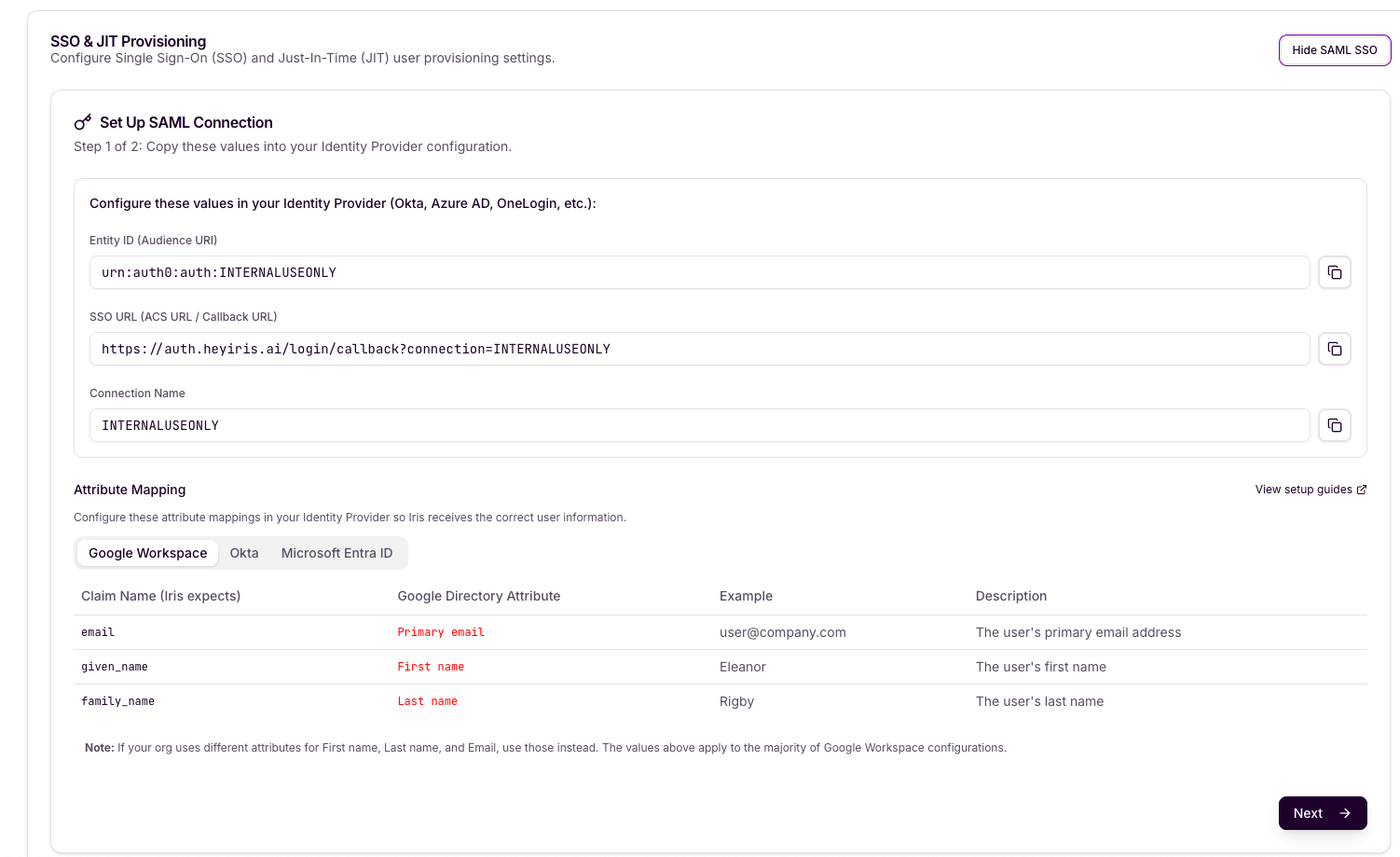
Copy each value using the copy button next to the field and paste them into the corresponding fields in your Identity Provider's application settings.
Add second org-specific identifier urn:auth0:heyiris-prod:<CONNECTION> as an Identifier in your Enterprise Application alongside the existing one:
Azure Entra → Enterprise App → Single sign-on → Identifier (Entity ID)
Okta → SAML app → Audience URI (SP Entity ID)
Google Workspace → SAML app → (Entity ID)
OneLogin → SAML app → Audience (EntityID)
Attribute Mapping
Configure the following attribute mappings in your Identity Provider so Iris receives the correct user information. Select your IdP below for the relevant attribute names:
Google Workspace
Okta
Microsoft Entra ID
Note: If your org uses different attributes for First name, Last name, and Email, use those instead. The values above apply to the majority of configurations.
Provide XML Metadata
In this step, you will supply Iris with your Identity Provider's metadata. This tells Iris how to communicate with your IdP for authentication.
Choose one of the two methods to provide your IdP metadata:
Recommended: Metadata URL
Metadata XML: Paste your IdP's SAML metadata XML directly if a URL is not available.
Using Metadata URL (Recommended)
Enter your Identity Provider's SAML metadata URL in the IDP Metadata URL field. This is the URL where your IdP publishes its SAML metadata. Common examples:
Google Workspace example:
https://accounts.google.com/o/saml2/idp?idpid=<YOUR_IDP_ID>
Okta example:
https://<YOUR_DOMAIN>.okta.com/app/<APP_ID>/sso/saml/metadata
Entra ID example:
https://login.microsoftonline.com/<TENANT_ID>/federationmetadata/2007-06/federationmetadata.xml
Company Email Domain
Enter your organization's email domain (e.g., acmecorp.com). Users with this email domain will be automatically routed to this SAML connection when they log in to Iris.
Note: Do not include the @ symbol — enter the domain only (e.g., acmecorp.com, not @acmecorp.com).
Enable IDP-Initiated SSO (Optional)
Toggle this setting on if you want users to be able to start the login flow directly from your Identity Provider's application portal (e.g., an Okta dashboard or Google app launcher), rather than always starting from the Iris login page.
Completing Setup
Once all fields are filled in, click "+ Create Connection" to finalize the SAML connection. Iris will verify the metadata and activate SSO for your organization.
After setup is complete:
Users with your configured email domain will be automatically routed to your SSO login when they click Sign in with SSO from the Iris Login page (https://studio.heyiris.ai/login)
New users who authenticate via SSO will be provisioned automatically (JIT provisioning).
You can view or hide the SAML SSO configuration at any time from the SSO & JIT Provisioning section in your org settings.
You can choose what role to give JIT-provisioned users within Settings > Security as well
Need Help?
If you encounter issues setting up SSO that are not covered in this guide, please reach out to your Iris CSM or contact Iris support at support@heyiris.ai